Best Practices to Protect Your Mobile Application Penetration Testing
Ah, mobile apps! They’re like our little pocket-sized helpers, ready to assist us at a moment’s notice. But with great power comes great responsibility, and that includes keeping these apps safe from cyber threats. Enter mobile application penetration testing, the caped savior of the cybersecurity world. This mighty practice involves simulating a cyber-attack on your app to identify potential vulnerabilities before the bad guys can exploit them.
Pen testing is crucial for keeping your app’s users and data safe. And if you’re not convinced yet, keep reading. This blog post will show you the ropes of mobile application penetration testing and how to keep your app’s security in tip-top shape.
So, buckle up and get ready to learn, because we’re about to take a deep dive into the world of mobile app security.
Planning and Preparation
Let’s get organized! Mobile application penetration testing requires a plan, just like a heist movie, but without cool gadgets and high-speed car chases. Here’s what you need to do:
- Set your goals and objectives. Do you want to find every single vulnerability in your app or just the most critical ones?
- Identify the testing scope. What parts of your app are you testing? What kind of data are you dealing with?
- Get creative and create test scenarios. It’s like writing your own little spy novel. Can your app survive a ransomware attack from a disgruntled ex-employee? Let’s find out!
- Gather your tools and resources. Assemble your own Avengers squad, but with software tools. You’ll need network scanners, vulnerability scanners, and brute-force tools. It might not be as exciting as fighting off an alien invasion, but it’s still pretty cool.
Remember, a solid plan is key to successful mobile application penetration testing. So get organized, get creative, and get ready to protect your app from potential cyber threats!
Conducting the Penetration Test
Now it’s time to put on your hacker hat and channel your inner Lisbeth Salander. It’s time to conduct the mobile application penetration test!
First, it’s time to execute those test scenarios you spent so much time creating. It’s like rehearsing for a play, except instead of reciting lines, you’re trying to break into your own app. If you’ve done your job right, you’ll be able to find vulnerabilities that you didn’t even know existed.
Once you’ve found those vulnerabilities, it’s time to put on your detective hat and start analyzing the results. This is where you get to play the role of Sherlock Holmes and try to piece together what went wrong. Did you forget to lock the door? Did you leave the window open? Or did you just forget to update your software? Whatever it is, it’s time to figure it out.
Last but not least, it’s time to report your findings. Think of it like writing up a secret mission report for your boss. You want to make sure you’re clear, concise, and accurate. Don’t forget to highlight the most critical vulnerabilities and provide recommendations for fixing them.
Mitigation and Remediation
It’s time to take action! You’ve conducted your mobile application penetration test and found some vulnerabilities. Now it’s time to fix them.
- Prioritize vulnerabilities like a to-do list and identify the most critical ones
- Develop a clear remediation plan like a battle strategy to fight off cyber criminals
- Implement security measures like fortifying your castle with firewalls and encryption
- Re-test and validate your app’s security measures like testing out a new recipe to ensure there are no vulnerabilities left open.
Mitigation and remediation are key to keeping your mobile app safe and secure. Just remember to stay vigilant and keep your sense of humor handy. It’s better to laugh in the face of potential cyber threats than to let them get the best of you!
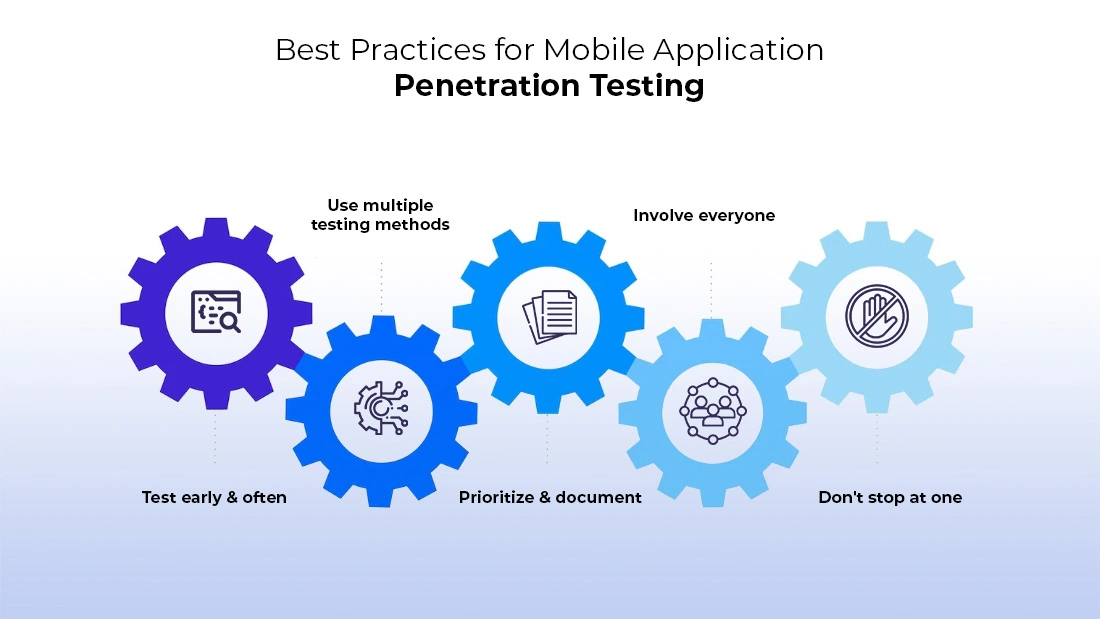
Best Practices for Mobile Application Penetration Testing
Now that you’re a mobile application penetration testing pro, it’s time to talk about best practices. These are the golden rules that will keep your app’s security in tip-top shape.
- Test early and often: Conducting penetration testing throughout the app development lifecycle is crucial to ensure that potential security vulnerabilities are identified and addressed as soon as possible. By doing this, you’ll save time and resources in the long run while keeping your app secure.
- Use multiple testing methods: It’s important to use a variety of testing methods and tools, such as network scanners, vulnerability scanners, and brute-force tools, to uncover potential vulnerabilities. This ensures that you’re covering all bases and not missing anything.
- Prioritize and document: Prioritizing vulnerabilities and documenting testing activities are essential to ensuring that you’re addressing the most critical issues first. By doing this, you’ll also be able to track your progress and use the information to improve your app’s security in the future.
- Involve everyone: Involving all stakeholders in the testing process is key to ensuring a well-rounded approach to mobile application penetration testing. This includes developers, project managers, quality assurance testers, and other relevant personnel. By doing this, you’ll get a better understanding of potential vulnerabilities and can address them more effectively.
- Don’t stop at one: Performing regular and comprehensive pen tests is crucial to staying ahead of potential threats. Hackers are always looking for new ways to exploit vulnerabilities, so it’s important to keep testing regularly to ensure that your app’s security is up-to-date and effective.
These best practices will help you stay on top of your mobile application penetration testing game. And don’t forget to have fun with it! What’s the point of saving the world from cyber threats if you’re not having a good time doing it?
Who can help You?

So now you know how to perform penetrating testing for mobile apps. But who can help you take it to the next level? Look no further than Beyond Key. Here’s why:
Unparalleled Expertise:
- Years of experience in mobile app testing
- A team of skilled professionals with extensive knowledge
Comprehensive Testing Solutions:
- Robust testing methodologies tailored to your app’s unique needs
- Rigorous testing across multiple platforms and devices
Swift Turnaround Time:
- Efficient processes that ensure quick delivery without compromising quality
- Accelerate your app’s time-to-market with Beyond Key
Proven Track Record:
- 98% client satisfaction rate speaks volumes about our success
- Trusted by top brands for their critical mobile app testing needs
Choose Beyond Key for flawless mobile app testing, unmatched expertise, and remarkable results. Join the ranks of satisfied clients who have experienced the Beyond Key difference. Don’t settle for the ordinary when the extraordinary is within reach.
Conclusion
Just remember, mobile app security is no laughing matter. In fact, it’s serious business. But that doesn’t mean we can’t have a little fun along the way. After all, a spoonful of humor helps the medicine go down.
And my final recommendation? Don’t be afraid to ask for help. If you’re not sure where to start, or if you need some guidance along the way, don’t hesitate to reach out to a professional. It’s like having a lifeguard at the pool, but instead of saving you from drowning, they’re saving you from potential cyber threats.
Mobile application penetration testing is a critical part of keeping your app’s security in check. And with the right planning, preparation, and execution, you can ensure that your app is as safe as possible. Now go forth, test, and conquer!