Cloud Penetration Testing: A Practical Security Testing Guide
Businesses are operating, scaling, and innovating on the cloud. As more organizations move to the cloud, there is a growing need for robust data security measures. Cloud adoption is the new normal across the globe. It offers productivity and allows businesses to work 24/7.
Whether you work on a public, private, or hybrid cloud model, adopting traditional security measures is not enough. In this blog, we will look at how cloud penetration testing services can help you identify
Worldwide Security Spending to Increase by 12.2% in 2025 as Global Cyberthreats Rise, Says IDC
What is cloud penetration testing?
Cloud penetration testing is a simulated cyberattack on cloud environments (PaaS, SaaS, IaaS). It is a security assessment conducted by an in-house team to identify vulnerabilities and misconfigurations, and to accelerate security remediation paths. Cloud pen testing is designed to manage risks, weaknesses, and threats.
What’s the objective of cloud pen testing? It’s protecting the cloud infrastructure from ever-evolving threats and improving the cloud security from any cyber-attacks in the future. This approach focuses on IAM policies, multi-cloud architectures, APIs, containers and on shared responsibility models.
It evaluates Container and Kubernetes vulnerabilities, misconfigured storage buckets, insecure APIs, lateral movement opportunities, data exposure risks and more. In this guide, we’ll walk through what cloud security penetration testing involves, how a practical cloud pentesting methodology works, and why more organizations are treating it as a critical part of cloud security strategy.
Cloud penetration testing methodology
A structured cloud penetration testing methodology helps you identify risks of data breaches. Every undesired activity is based on scope and cloud environment. Here are the key phases of cloud based penetration testing .
Scoping and Planning
Mention why you need this testing, state your objectives, and what the rules of engagement are. This step includes defining compliance requirements, APIs, and cloud sources to ensure testing aligns with security goals.
Data collection
This step includes collecting data. From current assets to configurations, from access control to entry points, exploring data can help you build a clear picture of the potential attacker.
Threat modeling
Here, you can identify potential attackers by understanding threat scenarios, cloud architecture, sensitive data sets, and related information.
Assessment of vulnerability
Misconfigurations exposed services and insecure permissions. You can trace attack paths across accounts, services, and the network to identify the attacker.
Penetration testing
Tech experts replicate real-world cyber breach scenarios to evaluate impact and validate risks. This reveals how the attacker can gain access to the organization’s data environment.
Analyze risk and report it
Create a detailed risk report. Document your findings and mention the proof of concept, business impact that can help prioritize the errors.
Retesting and validation
Validate remediation and identify issues. Confirm the vulnerabilities and support compliance requirements.
80% of cloud breaches are caused by basic mistakes. Source: ITPro
What are the types of cloud pen testing?
Ethical hackers, also known as white-hat hackers work with organizations to identify vulnerabilities in their IT environment. Let’s have a look at the types of pen testing methods.
- White-box testing:
- Gray box testing
- Black-box testing
White-box pen testing
It allows testers to access the IaC templates and credentials. They have access to code and configurations. This audit type helps you find misconfigurations in CI/CD pipelines, Terraform, IAM and CloudFormation.
Gray-box pen testing
Gray-box testing provides testers with partial access to documents and/or user credentials. It simulates an attacker and helps reveal vulnerabilities related to privilege escalation, access controls, and lateral movement.
Black-box testing
Testers have no prior information about the data environment. They replicate the process an external hacker uses, including public API, DNS enumeration, OSINT, etc. This method helps you understand how reachable your public-facing assets are by testing perimeter defenses and entry points.
Security spending is expected to see growth throughout the 2023–2028 forecast period, reaching $377 billion in 2028. Source: IDC
What are the 8 Cloud Security Threats You Should Be Aware Of?
- Misconfiguration: not properly configured permissions, storage, security settings, and cloud resources.
- Unauthorized Access: weak passwords and credentials, identity controls, and more can open doors for cyber-criminals to barge in.
- Insecure Interfaces and APIs:
- Data Loss: Accidental deletion of data, breaches due to improper/inaccurate backups, and more.
- Malware: Malware can pass through the cloud workload through applications and data.
- Shared Technology Vulnerabilities: Organizations rely on shared infrastructure or multi-tenant environments, which can bring in data-related risks.
- Insider Threats: Whether contractor, partners, or employees, anyone with privileged access to sensitive business information can intentionally or unintentionally expose it.
- Lack of visibility: Detecting threats, misconfigurations, or suspicious activity can be difficult if there’s limited data monitoring
Beyond Key assisted a leading US-based IT support provider with black-box penetration testing services.
Challenge: They were going through frequent failed login attempts from attackers. Sensitive files were accessed by public. Admin panel lacked brute-force protection. They had unclear resilience against OWASP Top 10 vulnerabilities.
Solution: Beyond Key is backed by professionals with certifications such as Certified Ethical Hacker Master, Azure Network Engineer Associate, eLearnSecurity Junior Penetration Tester Version 2 and many such courses. They conducted a thorough black-box penetration test to uncover hidden risks and vulnerabilities.
Download the case study
What are the benefits of cloud pen testing?
Whether you use public cloud, private cloud, or a hybrid cloud model, penetration testing helps organizations identify vulnerabilities, validate controls, and measure data exposure.
1. Secure your confidential business data
By following a structured cloud pen testing approach, you can help detect misconfigurations and exposed assets before an attacker intrudes.
2. Reduce business expenses
Investing in cloud penetration testing services can help your organization save time and effort. Human testers can focus on higher-level activities.
3. Meet security compliance requirements
Regular penetration testing can support compliance efforts for standards and regulations such as PCI DSS, HIPAA, ISO 27001, and more.
Real-world scenario:
Compromised IAM Roles & Privilege Escalation
Scenario:
A cloud-based organization relied on IAM roles for services in GCP.
Findings:
- EC2 instance has overly permissive IAM role (*:*)
- Attacker gains shell access via vulnerable web app
- Uses metadata service to extract IAM credentials
Penetration Testing Focus:
- Accessing instance metadata (169.254.169.254)
- Enumerating IAM permissions
- Privilege escalation techniques
Impact:
- Full account takeover
- Ability to spin up resources, access databases, and exfiltrate data
Learning Outcome:
Highlights risks of poor identity and access management.
What are the top cloud pen testing providers?
Let’s have a quick look at the top 5 cloud penetration service providers:
- Rhino Security Labs: Offers custom tools such as Pacu and is known for AWS pen testing.
- Beyond Key: Global consultancy with specialized expertise in multi-cloud security platforms.
- Bishop Fox: Leaders in detailed cloud assessments. Cosmos platform helps them perform continuous testing.
- NetSPI: Offers seamless API/container testing and PTaaS on Azure, AWS, and GCP platforms.
- Cobalt: Known for offering on-demand PTaaS for cloud infrastructures.
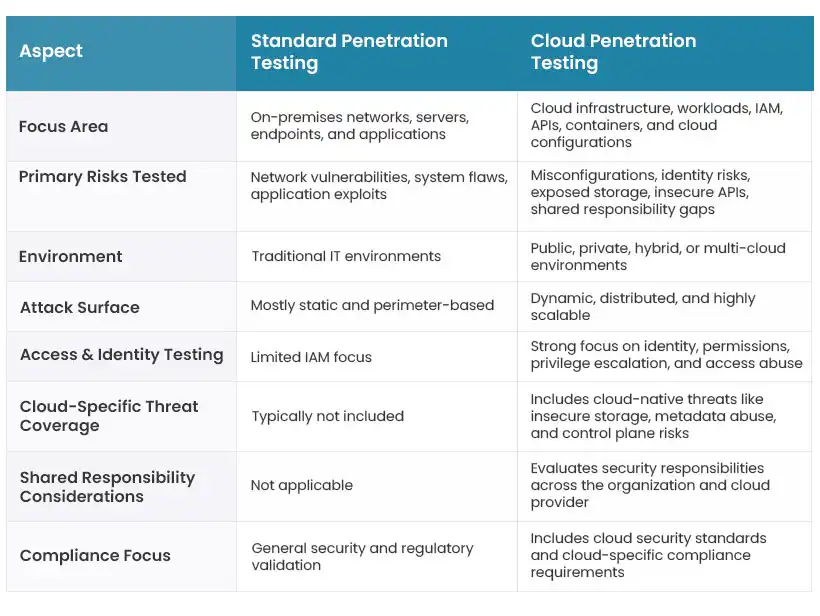
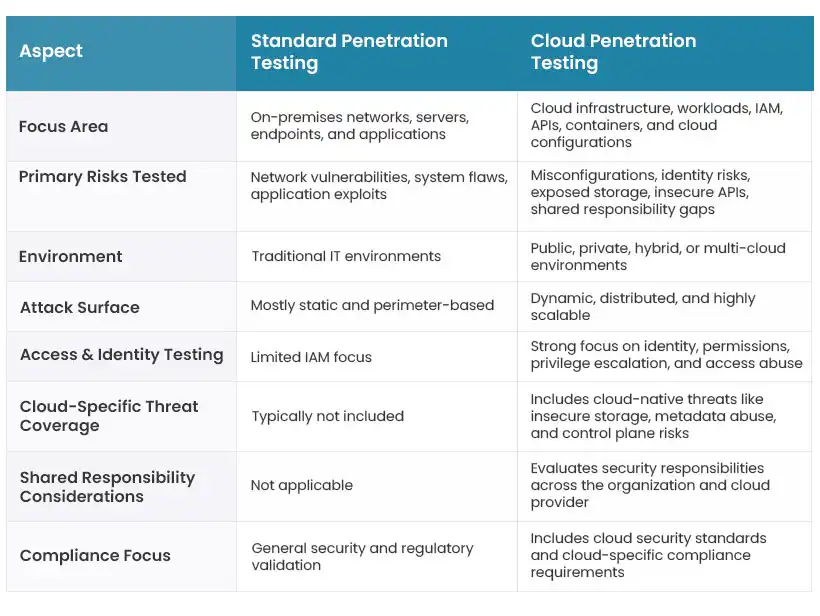
What is the difference between traditional testing and cloud pen testing?
While both approaches aim to identify and exploit security weaknesses before attackers do, cloud penetration testing addresses risks unique to cloud environments that traditional testing may not fully cover.
Final Thoughts
Cloud penetration testing helps organizations uncover vulnerabilities, strengthen data security, and support compliance. Cloud threats are evolving every day. Therefore, it has become critical for organizations to future-proof their critical data and improve their cloud security posture.
If you want to learn more about cloud security and penetration services, please reach out to us here. Beyond Key is a leading cloud consulting service provider with multiple Fortune 500 companies as their clients.
Frequently Asked Questions
1. What is cloud penetration testing?
Cloud penetration testing is a simulated cyberattack. The purpose of this simulation is to identify security gaps, vulnerabilities, and misconfigurations in cloud environments.
2. Why is cloud penetration testing important?
It helps businesses reveal security weaknesses before invaders do. It focuses on cloud security controls while minimizing supporting compliance requirements.
4. How is cloud penetration testing different from traditional penetration testing?
Traditional penetration testing focuses on locally hosted infrastructure.
Cloud penetration testing focuses on cloud-specific risks such as exposed storage, IAM misconfigurations, insecure APIs, and more.